What is an account takeover attack? ATO fraud detection and prevention
Account Take-over or Account Takeover Fraud and why it’s not the same as identity theft.
The definition of account takeover (ATO) or account takeover fraud is obtaining a legitimate user’s details to take over their online accounts, possibly enabling monetary or credit card theft. ATO can happen with an automated script that enters the credentials en masse or with a human typing them and accessing the account. The goal of ATO is to make a profit using the value of the account.
What are the risks of account takeover?
When bad actors take over a user account, they can roam free in the environment and make all sorts of fraudulent activities. These activities can go from updating a shipping address or changing a password to making fraudulent purchases (in eCommerce) or money movements (in financial institutions) – these are considered to come from account takeover fraud as opposed to identity theft. The consequences for businesses affected by ATO are endless, but the main ones are increased chargebacks, increased customer transaction disputes, loss of customer trust, customer churn, and brand damage. Often, without a customer claim, a company may not realize such a takeover happened. For an eCommerce company, chargebacks are especially damaging as they have to refund the legitimate client for the fraudulently purchased goods, even though the company won’t retrieve the product. This affects the company’s chargeback rate; the number of chargeback requests a company receives compared to their total sales. When this rate is high, it means that there are more chargeback requests than allowed and the payment processing companies raise the processing fees for each of that company’s transaction. This can translate into millions of dollars in losses. For financial institutions, fraudulent money movements and other malicious activities affect their customer directly but can also be a sign of money laundering. Without protection on the account, money can be moved from one account to another without leaving a trace. Some financial institutions using a solution such as Vocalinks’, a Mastercard company, can trace these activities and see exactly where the money ended and what network it belongs to – and often retrieve it. For both eCommerce and financial companies, account takeover is a black hole sucking their brand image and customer trust, affecting the company’s top and bottom lines.
https://nudatasecurity.com/resources/blog/evolution-of-ato-or-how-humans-are-now-replacing-bots/
Account takeover vs. identity theft: what’s the difference?
As we mentioned earlier, account takeover (ATO) is when someone knows someone else’s username and password and accesses their account. Synthetic identity is when someone knows someone else’s details (name, last name, address, date of birth, etc.) and opens a new account under that person’s name. With this definition, they may seem similar as they both use someone else’s information maliciously, but it’s important to be alert to a crucial difference. Here is an example: Let’s imagine that you have this information from your neighbor:
- First name
- Last name
- Address
- Date of birth
- Email password
Maybe you also know other bonus information like your neighbor’s employer, her city of birth or her social security number. Now, question time: what do you do with that information? A: You take the username and password and access your neighbor’s email account: In this case, you are taking over an account because you are entering an existing account that belongs to someone else. B:: Instead of taking over an existing account, you take her personal information and create a new account or a new application to ask for credit. In this scenario, you are stealing an identity because you are not using an existing account; you are using her information to create a new one as if your neighbor was opening it. In this case, you are stealing an identity to pretend you are someone else and creating a new account. In both situations, you need to have the other person’s information, but what you do with this information determines whether it is account takeover or identity theft.
How does account takeover happen?
Account takeover starts days, weeks or months before the customer finds a fraudulent transaction. Without a tip-off line to check on unusual activity, detection and prevention are hard because it starts when a bad actor buys a set of breached personal data such as username and password. Fraudsters may try to attack login interfaces in an automated fashion, with data stolen through a phishing attack or a previous database hacking, and test them against other web services. By running a script against the login interface, they can test thousands of username and password combinations per second and find the working pairs. Once they find the “good” combinations, they either go ahead and take over the accounts right there and then or resell those verified credentials for a higher price in the dark web, as verified credentials are more valuable. This process taking place behind the scenes usually happens without businesses noticing it, making protection harder. Normally, the first time the attack surfaces is after the fact; when the legitimate user realizes something happened in their account.
What type of data is used for an account takeover?
 The data required to take over an account depends on the information each site needs to verify their user. If an account only requires a username and password, then those two data points are enough. But if the account requires a username, password, and a one-time code, or a biometrics verification (such as a fingerprint scan or iris scan), then the fraudster will need to access that information to take over the account. One-time passwords (OTP) and physical biometrics are harder to access for the average fraudster, but someone specialized can get a hold of them or, for example, intercept an SMS with the one-time code (OTP). This is why relying solely on data, or physical identifiers is no guarantee of safety.
The data required to take over an account depends on the information each site needs to verify their user. If an account only requires a username and password, then those two data points are enough. But if the account requires a username, password, and a one-time code, or a biometrics verification (such as a fingerprint scan or iris scan), then the fraudster will need to access that information to take over the account. One-time passwords (OTP) and physical biometrics are harder to access for the average fraudster, but someone specialized can get a hold of them or, for example, intercept an SMS with the one-time code (OTP). This is why relying solely on data, or physical identifiers is no guarantee of safety.
How does account takeover make a profit?
We talked about bad actors changing the user’s password or shipping address, for instance, but these are not direct ways of making profit, just preambles.
What is credit card fraud?
By definition, credit card fraud is the most popular way to make money from stolen credentials. The bad actor makes fraudulent purchases with the legitimate user’s stored credit card or with information from a stolen credit card. This means that bad actors either use the credit card available on the account or, if they don’t want to be flagged by the account owner, they simply use a credit card number they’ve purchased off the dark web.
What is loyalty fraud?
Loyalty fraud, also known as rewards fraud, rewards abuse, and interaction fraud, is when a bad actor cashes the legitimate user’s stored points rewards, miles – or another type of company-provided benefits – to make a monetary profit. This way of making a profit from account takeover has been gaining muscle because of its discretion. Loyalty fraud is on the rise because users don’t monitor their points as often as they check their credit card transactions. They also may have an alert set up for suspicious credit card transactions but not loyalty account transactions. This gives bad actors more time to commit fraud before they get caught.
What is bank account fraud?
Bank account fraud is one of the most commonly occurring type of account takeover fraud. It happens when an unauthorized person takes over, or gains access to someone else’s bank account. Once in the account, the bad actor can send money out to a new payee, or, if they are amateurs, even pay their bills directly. They will often change the password right away to make sure they have enough time to drain your account before you access it.
Who are the targets?
If your company has accounts, then it’s exposed to account takeover. Simple as that. Account takeover attacks don’t discriminate against companies by their size, industry or location. Traditionally banks and credit card providers were the main victims, but an increase in “one-click payment” systems has made eCommerce and online retailers a large target. This is a fast-growing and widespread fraud. On the other hand, a classic small-company misconception is that “because I’m not a big fish, I’m probably OK.” Unfortunately, as long as a company has a login, a bad actor can and will use it. Fraudsters use the login interface to either test their purchased credentials or to access those accounts directly. In fact, small companies are sometimes less vigilant of unusual activity at login, account creation or password reset, making them a potentially more attractive target than bigger corporations. If you’re looking for an analogy, think of fraud as bike theft. A fancy bike is just as likely to be stolen as a cheap one; it just depends on how hard and risky it is to steal it and how much money the thief can make later from selling the bike without raising any flags.
How do I know I am a victim?
 You know you have an account takeover problem when you start getting a higher number of chargeback requests or fraudulent transaction claims. You can also predict you are going to be a victim of account takeover fraud if you see anomalous activity like hundreds of login attempts to access one account or password reset requests en-masse. These and many other signs that happen before a purchase or a transaction can tell you if a bad actor is at work. If you are a user, what you can do is check your accounts thoroughly. Look for a newly saved shipping address, credit card – or new payee, if you are looking at your bank account. Don’t forget to monitor your reward points as well, if you store any. You can also see if your email is compromised using pages like haveIbeenpwned.com.
You know you have an account takeover problem when you start getting a higher number of chargeback requests or fraudulent transaction claims. You can also predict you are going to be a victim of account takeover fraud if you see anomalous activity like hundreds of login attempts to access one account or password reset requests en-masse. These and many other signs that happen before a purchase or a transaction can tell you if a bad actor is at work. If you are a user, what you can do is check your accounts thoroughly. Look for a newly saved shipping address, credit card – or new payee, if you are looking at your bank account. Don’t forget to monitor your reward points as well, if you store any. You can also see if your email is compromised using pages like haveIbeenpwned.com.
How do I detect and stop it?
You need to be proactive instead of reactive to achieve account takeover detection and prevention. The account takeover solution doesn’t come by looking at the attacks after they happen: start looking for the pre-ATO signs today. Monitor your login, account creation or password reset placements. Look for unusual signs such as an account trying to be accessed several times in the last weeks. Or thousands of new accounts being created from one same IP, or location. Or check if the same type of device is triggering these unusual attempts. When you look into who is using your interface, whether successfully or not, you can find subpopulations and put those risky activities aside, interdict or stop them. Automate the process with a solution that can monitor your traffic 24/7. This is how you stop ATO before it ever enters your environment.
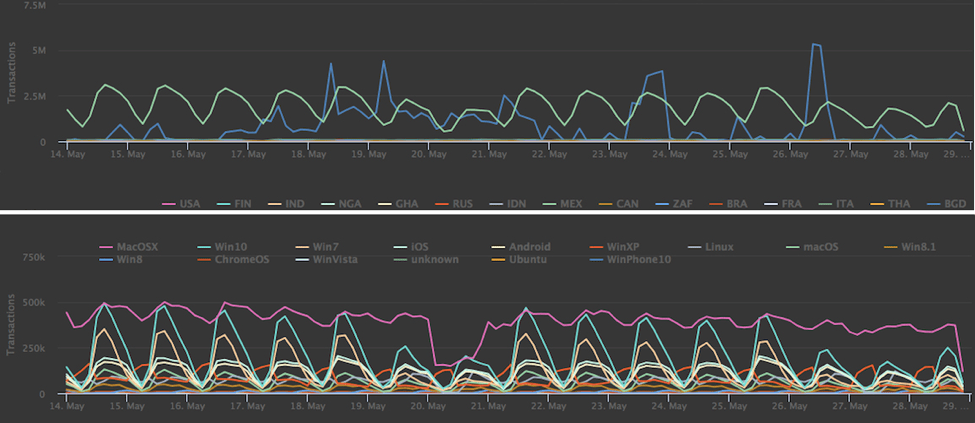
Country of origin of a session or operating system are some of the parameters you can analyze by drilling down in your environment.
https://nudatasecurity.com/resources/blog/mitigating-sophisticated-attacks-the-nudata-way-part-i/
Account takeover solution
Account takeover protection has to be carefully measured so you don’t insult good users and valued customers. In protecting our large eCommerce and financial institution clients, we often recommend an invisible solution placed at the pre-login stage such as ATO Protect. A pre-login tool monitors all the activity before it enters your secured environment. The user’s behavior determines if they are acting consistently, or if their behavior points to malicious intent. These solutions have a vast array of security sensors they monitor to assess the risk of an event in real time. Key data points that reveal early fraud include IP, location, connection, browser type, input type (is it a machine or a human?), the velocity of travel and hundreds of other signals. Behavioral analytics, which powers risk-based authentication, is a great way to ensure good users have a fluid online experience. Only riskier scores trigger further security countermeasures. Lastly, think of making it as easy as possible for customers to reach you if they suspect their account has been compromised.