Mitigating sophisticated attacks — the nudata way (part II)
This is the continuation of part I. If you haven’t read it, we suggest you start there for more attack types and fraud mitigation techniques.
Now, where were we? Right, we just talked about spotting human-driven attacks. Let’s look at how to spot probing attacks that sneak in, to learn from your security parameters.
1. Spotting probing attacks
Some of the most potentially damaging attacks we see on the nudata network start extremely small. By probing your defenses with a hard-to-detect, low-volume attack, a cybercriminal can ferret out your vulnerabilities without setting off any alarms. Then they use that knowledge to launch a larger attack tailored to your system’s specific weaknesses, hoping to overwhelm your defenses completely.
To prevent that from happening, early detection of probing is key. Think of those initial attacks as the first phase of a pest infestation. You might not notice or be bothered by the first ant scout who appears on a solo mission to find food in your kitchen. But you will definitely notice when there’s a several-feet-long trail of ants to the leaky pot of jam in your cupboard a day later. Intercepting that first ant takes extra work, but it saves you a lot of trouble in the long run.
Case study: On the trail of the cyber-ants
We recently mitigated a large multi-stage attack on a retail company in our network, in part by detecting the attackers’ initial probing. During this phase, which lasted one or two days, the attack was relatively small, just a small bump on a graph (you’ll see below). The attackers deployed human-like scripts that included realistic mouse movements and pauses between keystrokes to imitate human behavior. On an individual level, the probing attacks looked like legitimate traffic.
This was enough to fool the retailer’s bot-manager tool, which relied on comparing current data to known threats, such as IP addresses used in past attacks. However, nudata was able to detect the attack by looking at underlying patterns, such as anomalous behavior during the online interaction or an unusual number of login attempts within the same networks and IP addresses. After identifying the pattern, nudata blocked 99.8% of fraudulent login attempts, shutting down the first phase of the attack. (Unfortunately, there was more to come — the attack kept evolving, as you’ll see below.)
2. Mitigating evolving attacks
Attacks that begin with probing rarely stop there. The most sophisticated attacks we see in our network evolve quickly as they search for ways around their targets’ defenses. Such attacks can change strategies in as little as a day, so companies need to keep their threat models agile and adapt swiftly.
Case study: The cyber-ants become a swarm
The attack on the retail company we talked about earlier turned out to be an example of an evolving threat. After two days of probing, which nudata successfully mitigated, the attackers changed their strategy, refining their script to better mimic human behavior — for example, by creating a more natural rhythm of keystrokes. They also increased their attack volume, using an eye-popping 18,500 different IP addresses and ensured attack velocity remained low.
Ironically, doubling down on attacks makes nudata’s defenses stronger. The more a bad actor interacts with our client’s platform, , the more our solution learns. In this second phase of the assault on the retail company, nudata blocked 100% of attacks — an even higher success rate than we’d had during the initial probing.
We maintained this same mitigation rate even as the attack evolved into its third and final phase, with attackers doubling the number of IP addresses used in an attempt to evade detection. Despite the reduced velocity and fewer events per IP, nudata still identified patterns that revealed the attack, such as users holding their devices in ways that showed they weren’t human. All told, nudata blocked two million fraudulent logins in the last 48 hours of the attack — ending the cybercriminals’ attempt once and for all.
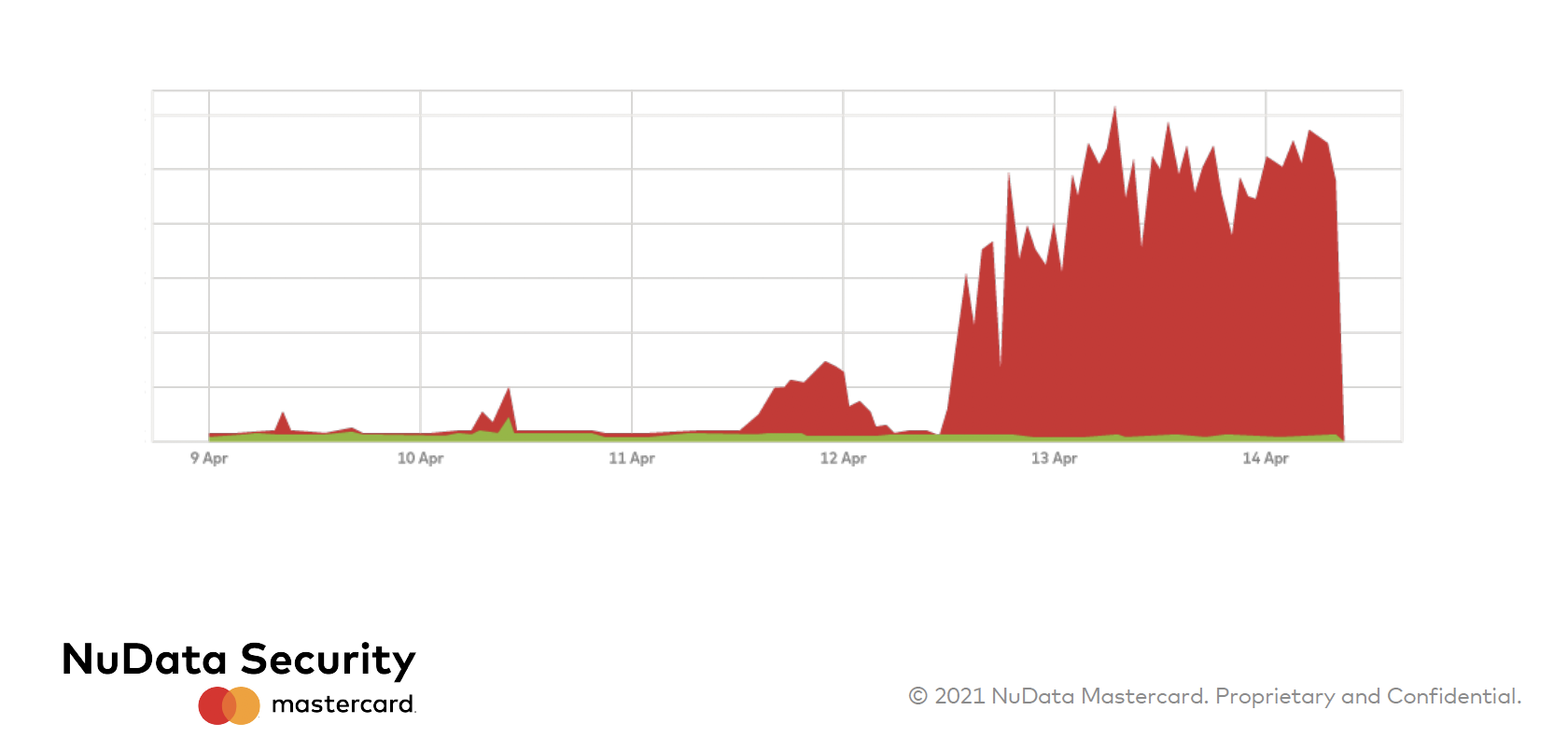
Fraudulent traffic (red) vs. legitimate traffic (green) over the course of a six-day evolving attack on a retail company
Preparing for the future of sophisticated attacks
Sophisticated attacks aren’t just growing more common — they’re also growing more creative. And it’s impossible to predict how they’ll continue to evolve. Cybercriminals are always dreaming up new ways to evade detection, and many standard bot-manager tools aren’t able to keep up, as we have seen in this article.
Ever-evolving attack strategies demand new, more agile defenses. By adopting multiple layers of security protection that can adapt alongside the threats you face, you’ll position your company to weather whatever challenges come its way.
More recent threat trends in our bi-annual report, Fraud Risk at a Glance.